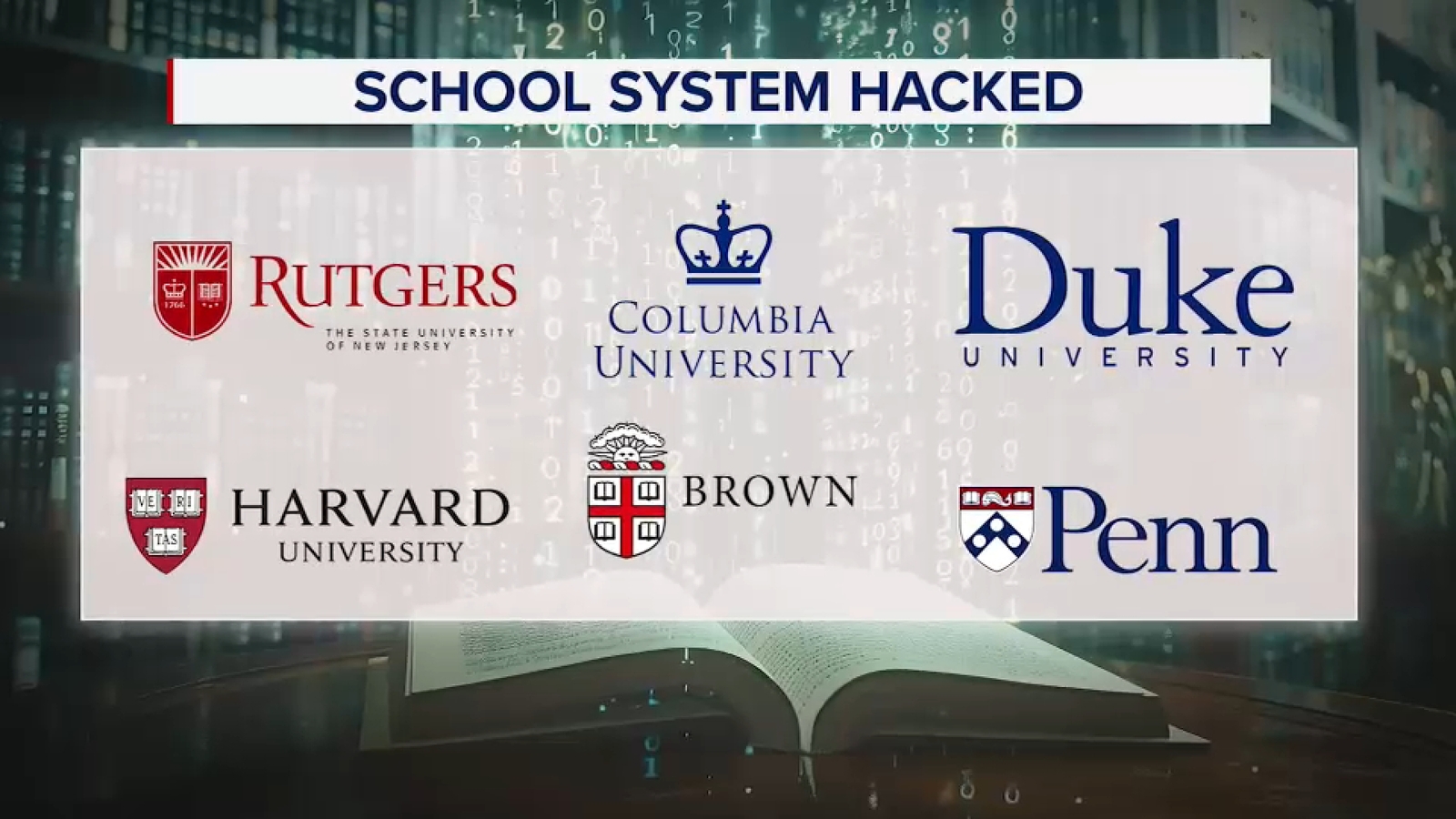
Canvas was disrupted by a cybersecurity incident that may have exposed personal information such as names, email addresses, phone numbers, student ID numbers and internal messages, affecting students at Columbia and other schools. Columbia said assignments and exams due Friday are postponed because of issues with Canvas and its courseworks platform. The breach is being linked to ShinyHunters, with reports that nearly 9,000 schools worldwide may have been affected.
This is a reputational and workflow shock more than a balance-sheet event for the edtech stack, but the second-order impact is meaningful: universities will likely accelerate redundancy planning for learning-management systems, secure messaging, and exam delivery tools over the next 1-2 procurement cycles. That favors vendors with stronger identity, monitoring, and incident-response layers, while raising scrutiny on “single pane of glass” platforms that become mission-critical during exam windows. The immediate loser is not just the compromised platform owner; it is any vendor perceived as operationally brittle when institutional downtime has visible academic consequences. The more important trading angle is the phishing tail risk. Exposed directory-level identity data materially improves spear-phishing conversion rates for 30-90 days, especially around grade release, financial aid, and transcript workflows. That raises downstream risk for university IT budgets, cyber insurance claims, and help-desk load, even if passwords were not exposed; the incident can still generate follow-on compromise costs that outlast the headline outage by a quarter or more. From a market perspective, this is supportive for cybersecurity incumbents and identity vendors rather than pure-play education software. The contrarian point is that these events often look larger socially than economically: buyers are slow, budgets are finite, and universities tend to renew on price unless a breach directly hits enrollment or compliance. So the near-term trade is on incident-driven sentiment and procurement headlines, not a durable rerating unless multiple institutions publicly switch vendors or insurers tighten underwriting for education tech. The cleanest risk/reward is a relative long in cybersecurity software versus education software, with a focus on names that benefit from identity hardening and phishing defense. If the breach chatter broadens to additional platforms or triggers formal investigations, expect a 1-2 quarter tailwind for security spend; if not, the move should fade as campuses normalize operations. The key catalyst to watch is whether procurement teams treat this as a one-off outage or a board-level data governance failure.
AI-powered research, real-time alerts, and portfolio analytics for institutional investors.
Request a DemoOverall Sentiment
moderately negative
Sentiment Score
-0.35