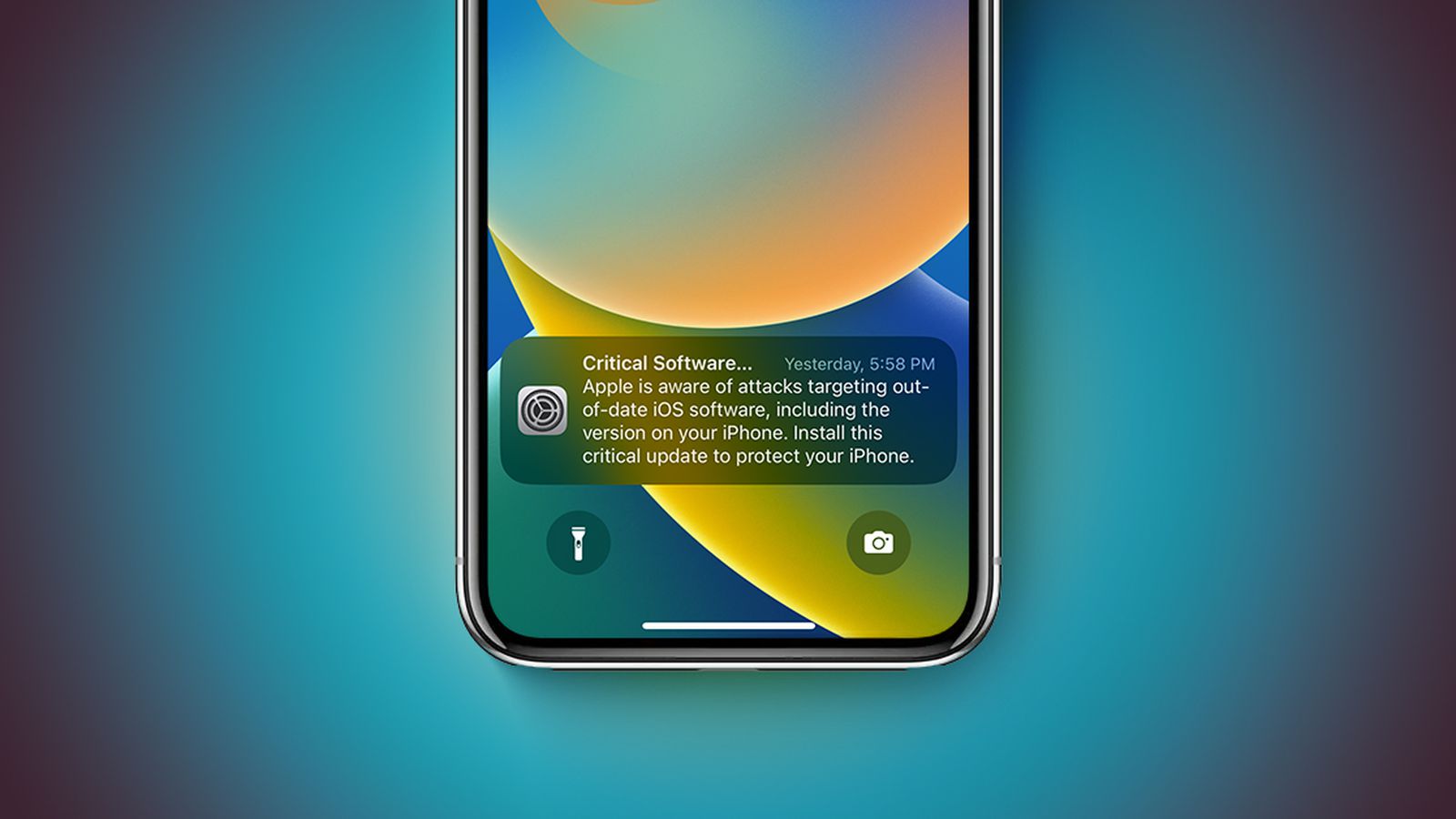
Apple is sending Lock Screen “Critical Software” alerts to iPhones and iPads on older iOS/iPadOS versions warning of active web-based attacks exploiting Coruna and DarkSword (affecting iOS 13 through iOS 17.2.1). Apple released iOS 15.8.7 and iOS 16.7.15 on March 11 to address Coruna; devices on the latest updated builds of iOS 15+ through iOS 26 are protected while iOS 13/14 devices must upgrade to iOS 15 to receive fixes. Safari’s Apple Safe Browsing blocks identified malicious domains by default, and Apple recommends enabling Lockdown Mode (iOS 16+) for devices that cannot update.
This episode should be read as a demand signal rather than a pure product-quality shock: elevated visibility of mobile web exploits tends to accelerate OS upgrade rates and forces incremental security spend across both consumer and enterprise channels. Expect a measurable bump to upgrade-driven device replacement over a 6–18 month horizon concentrated among users on multi-year-old hardware, which mechanically benefits foundry/assembly suppliers with capacity to absorb a modest uptick in unit demand. On the security spend side, incidents that weaponize the browser ecosystem shift budgets from perimeter-only solutions to endpoint and mobile-specific telemetry—an area where cloud-native vendors with mobile SDKs and telemetry pipelines can monetize quickly within 3–12 months because procurement cycles are shorter for point solutions than for full-platform rip-and-replace projects. Conversely, any near-term reputational noise for the platform owner is likely transitory; meaningful downside would require sustained exploitation at scale or regulatory/legal escalation, which is a lower-probability multi-quarter tail event. The biggest second-order risk is policy and procurement: sustained headlines could prompt carriers, carriers’ app stores, and enterprise MDM vendors to harden app delivery and push forced updates, creating winners among firms that supply MDM, app vetting, and secure-browsing overlays. Monitor patch-adoption curves (weeks), exploit sightings and domain-block lists (days–weeks), and replacement orders at device assemblers (quarterly) to time exposure and hedge accordingly.
AI-powered research, real-time alerts, and portfolio analytics for institutional investors.
Overall Sentiment
neutral
Sentiment Score
0.00
Ticker Sentiment