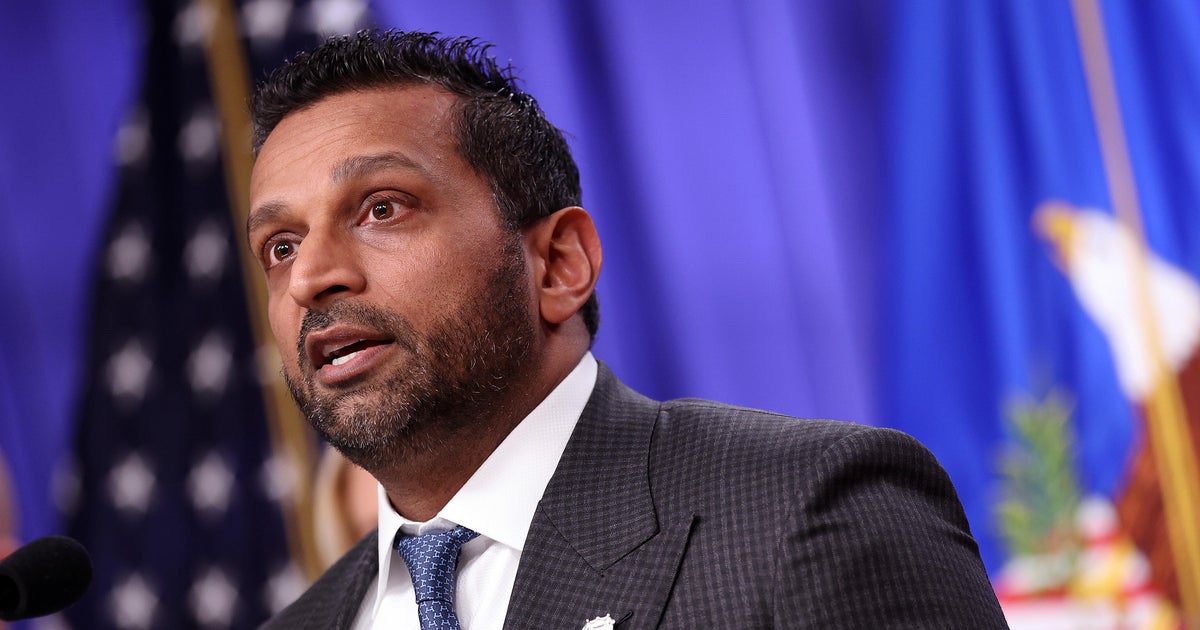
FBI Director Kash Patel's personal email was breached by Iran-linked hackers (Handala HackTeam), who posted photos and a purported resume after the Justice Department earlier seized four domains tied to the group. The domain used in the Patel hack was registered on March 19, the same day as the DOJ seizures; Handala has been linked to prior malware attacks and to posting data on ~190 individuals connected to Israeli defense. This is a direct national-security cyber incident that raises security and reputational risk and may modestly boost attention to cybersecurity and defense contractors but is unlikely to move broad markets.
This episode should be read as a catalyst for durable re-allocation of incremental spending rather than a one-off event. Expect procurement timelines to compress: federal and enterprise buyers historically shift from multiyear RFP cycles to accelerated tactical buys within 3–9 months after high-profile compromises, favoring endpoint detection, identity, and managed detection & response (MDR) vendors that can demonstrate rapid time-to-value. Supply-chain and hardware-attestation vendors are a second-order beneficiary that receives little attention in market moves focused on software names. Demand for secure element, logging integrity (WORM), and HSM-backed key management typically rises 6–18 months after an uptick in attribution risk because buyers seek cryptographic proofs that software-only controls can’t provide. The insurance and legal ecosystem will reprice: we should expect a mix of higher premiums and stricter exclusions that crystallize over 9–15 months, creating a transient revenue tailwind for carriers that raise prices successfully but a hit to buyers who self-insure. Simultaneously, defense primes with established cyber-offense/defense contracting lines become a safer play for policy-sensitive allocators; their backlog and bid pipelines react on a multi-quarter cadence. Market reactions are often binary and short-lived; pure-play software names are prone to overshoot on both upside and downside. Tactical positions that capture the shift to cloud-native detection, hardware attestation, and disciplined insurers while hedging legacy-network exposure offer the cleanest risk-adjusted setup into a 6–12 month window.
AI-powered research, real-time alerts, and portfolio analytics for institutional investors.
Overall Sentiment
moderately negative
Sentiment Score
-0.60